Timely software patches are a powerful, cost-effective defense against evolving cyber threats. They reduce the window of exposure, shrink the attack surface, and support cybersecurity patching efforts across the enterprise. In practice, this means embracing software patch management, aligning teams, and prioritizing critical security patches. By weaving cybersecurity patching into daily operations and prioritizing those patches, organizations can improve resilience while controlling downtime and cost. From vulnerability remediation to governance reporting, a disciplined approach to patch management best practices strengthens security and trust.
Viewed through another lens, this topic can be described using terms like security updates, proactive bug fixes, and a steady vulnerability management cadence that shrinks exposure before attackers act. A structured remediation timeline and patch automation ensure teams move beyond reactive patching toward consistent, governed maintenance. Framing the practice as risk-based remediation, continuous software maintenance, and governance-driven patching helps executives understand the value of timely actions. Latent Semantic Indexing principles suggest using related terms such as vulnerability management, patch cadence, security updates, and patch automation to capture broader security conversations.
The Critical Role of Timely Software Patches in Cybersecurity
Timely software patches are one of the most cost-effective controls in cybersecurity. By closing known flaws and rapidly applying fixes, patching directly reduces the attack surface and accelerates vulnerability remediation across operating systems, applications, and plugins. Integrating timely patches into a comprehensive software patch management strategy strengthens defenses and aligns with patch management best practices.
When organizations delay patches, they create predictable risk windows that threat actors can exploit. The speed of remediation matters as much as patch quality, especially for critical security patches that appear in public advisories. A disciplined approach helps meet regulatory expectations, reduces the likelihood of data breaches, and supports a stronger security posture overall.
Establishing a Patch Management Foundation: Visibility, Inventory, and Prioritization
A robust patch management program begins with visibility. Building a complete asset inventory that catalogs hardware, software versions, patch levels, and configurations is essential for effective software patch management. This clarity enables teams to identify vulnerable endpoints and track which patches are pending, setting the stage for timely remediation.
Regular vulnerability scanning and risk assessment turn patching into a data-driven effort. By prioritizing patches according to severity, exposure, and asset criticality, teams can focus cybersecurity patching on high-risk systems first while maintaining comprehensive coverage across the environment.
From Vulnerability Discovery to Remediation: The Patch Deployment Lifecycle
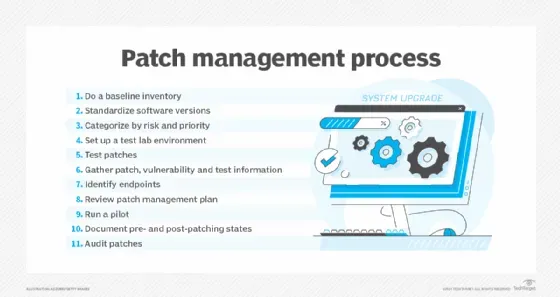
Vulnerability discovery should trigger a structured remediation workflow that follows a disciplined patch deployment lifecycle. Testing patches in controlled environments minimizes compatibility issues and operational disruptions. Patch management best practices emphasize change control, backups, rollback plans, and clear documentation of approvals.
Deployment should proceed in staged phases—from pilot deployments to broader rollouts—followed by verification that patches installed correctly and that applications continue to function as intended. Automated verification and continuous monitoring help confirm success and provide evidence for audits and compliance reporting.
Best Practices for Efficient Patch Management Across Environments
Effective patch management spans on-premises, cloud, and hybrid environments. Standardizing processes, leveraging centralized consoles, and embracing automation where appropriate accelerates detection, testing, and deployment while preserving stability. A consistent patch cadence is a hallmark of strong cybersecurity patching across the enterprise.
Documentation and governance underpin ongoing compliance and audit readiness. Aligning patch management with regulatory requirements and industry standards demonstrates mature cybersecurity hygiene and often improves vendor support outcomes due to reliable patching records and repeatable processes.
Automating Security Patching: How Automation Accelerates Timely Patches
Automation is a cornerstone of speed and scale in patch programs. Automating asset discovery, vulnerability scanning, deployment, and post-deployment verification reduces manual effort and improves the timeliness of patches—crucial for timely software patches and overall patch management efficiency.
However, automation must be balanced with governance and human oversight. Maintain testing environments, implement approval workflows for high-impact fixes, and deploy dashboards that highlight risk trends to ensure automation accelerates remediation without compromising change control.
Measuring Success: Metrics and Case Studies for Patch Programs
Measuring the effectiveness of a patch program requires relevant metrics and key indicators. Common KPIs include mean time to patch (MTTP), patch success rate, unpatched asset counts, and the rate of vulnerability remediation across severity classes. Linking these metrics to risk reduction clarifies the business value of timely software patches.
Case studies illustrate how disciplined patch programs reduce incidents and improve compliance. Organizations that implement timely software patches, adhere to patch management best practices, and maintain unified patching strategies typically report fewer exploit attempts, faster remediation cycles, and a stronger overall cybersecurity posture.
Frequently Asked Questions
Why are timely software patches essential for cybersecurity patching?
Timely software patches close known vulnerabilities quickly, reducing the attack surface and shrinking exploit windows. In cybersecurity patching, prompt remediation minimizes the chance that attackers exploit gaps. Prioritizing timely patches is a foundational element of an effective patch management strategy.
What are patch management best practices to ensure timely vulnerability remediation?
Adopt a repeatable process: maintain an up-to-date asset inventory, run regular vulnerability scans, and use risk-based prioritization to focus on critical security patches. Test patches in a controlled environment, apply clear change controls, and deploy in staged rollouts with verification and monitoring. This reflects patch management best practices to deliver timely vulnerability remediation.
How does vulnerability remediation relate to patch timing in practice?
Vulnerability remediation is most effective when patches are applied promptly. Delays extend the window of exposure, especially for critical security patches that are actively exploited. A risk-based approach ensures the most dangerous flaws are remediated first, aligning patch timing with threat reality.
How can organizations structure a software patch management program for reliability and speed?
Build governance and visibility around patching: map assets, set SLAs based on severity, automate discovery and deployment where feasible, and implement testing, backups, and rollback plans. Use a staged rollout and ongoing monitoring to balance speed with stability—core patch management best practices.
What role do automation and testing play in timely patch deployment?
Automation accelerates discovery, deployment, and verification across endpoints, reducing manual effort and drift. Testing helps catch compatibility issues before production, preventing downtime. Together they enable timely software patches without compromising reliability.
What metrics show a successful timely patch program?
Track metrics such as mean time to patch (MTTP), patch success rate, unpatched asset counts, and regular compliance reporting. These signals show how effectively your timely patch program reduces risk and demonstrates vulnerability remediation progress.
| Topic | Key Points |
|---|---|
| Introduction |
|
| The Reality of Vulnerabilities and Patch Management |
|
| Why Timeliness Matters for Security |
|
| Establishing a Patch Management Foundation |
|
| The Security Benefits of Timely patches in Practice |
|
| Balancing Speed with Stability |
|
| Operational and Business Benefits Beyond Security |
|
| Practical Steps to Build a Timely Patch Program |
|
| Common Challenges and How to Overcome Them |
|
| Case Example: A Secure Patch Cadence in Action |
|
Summary
The table above outlines the essential points from the base content, highlighting why timely patches matter, how to build an effective patch management program, and the concrete benefits across security, operations, and governance. A structured approach to patching can reduce risk, improve resilience, and support business continuity.