Cloud and On-Prem Patch Strategies unite organizations that run workloads across public cloud and on‑prem infrastructure, aligning governance with coordinated patch delivery. A cohesive approach covers cloud patch management and on-premises patching best practices, reducing exposure and downtime. By harmonizing updates across environments, these strategies lower risk, improve compliance, and boost resilience in a hybrid patch management landscape, including security patching for hybrid environments. Automation, visibility, and a single source of truth enable proactive vulnerability management across cloud and on-prem assets, aligning patch management in hybrid cloud environments with on‑premises patching best practices. With a governance‑led, risk‑aware deployment model, organizations can patch faster while maintaining reliability.
From an LSI-inspired perspective, the topic is described using alternative terms such as cross‑environment vulnerability management, unified patch governance, and hybrid IT patching strategy. In this framing, organizations synchronize cloud patch management with on‑premises patching best practices under a single risk and compliance framework, preserving consistency across the hybrid stack. The emphasis shifts to scalable automation, integrated inventories, and phased deployments that span clouds and data centers.
Understanding Hybrid Patch Management: Aligning Cloud and On-Prem Patch Efforts
In hybrid patch management, organizations must orchestrate updates across public cloud workloads and on‑prem infrastructure. This requires recognizing that cloud patch management often leverages image refreshes, platform updates, and managed services, while on‑prem environments rely on traditional patch catalogs and deployment tools. By acknowledging these dual realities, teams can design a cohesive strategy that minimizes drift and accelerates remediation across both footprints.
A well‑rounded approach to hybrid patch management emphasizes governance, risk, and automation to harmonize cloud patch management with on‑premises patching best practices. The goal is to reduce exposure to vulnerabilities while maintaining uptime and agility. Integrating continuous vulnerability management and synchronized patch catalogs helps ensure that security patching for hybrid environments remains consistent, scalable, and auditable regardless of where assets reside.
Establishing Inventory and Visibility for Cloud Patch Management in Hybrid Environments
Visibility is the cornerstone of effective patching in hybrid environments. Start with comprehensive asset discovery across cloud accounts, virtual machines, containers, storage systems, and on‑prem servers. An authoritative CMDB or asset registry should track hardware, software, patch levels, dependencies, and owners to enable accurate reporting and prioritization.
With Cloud and On-Prem Patch Strategies, a single source of truth feeds risk scoring, patch catalogs, and deployment pipelines across environments. A robust vulnerability management program prioritizes patches by exposure and business impact, while an integrated change‑management process ties patch activity to approvals, testing, and rollback plans. This level of visibility is essential for maintaining security patching for hybrid environments.
Cloud and On-Prem Patch Strategies: One Governance, One Risk Framework
This subheading emphasizes a unified approach: one governance model, one risk taxonomy, and a consistent patch life cycle that spans both cloud and on‑prem resources. Establishing standardized policies helps reduce drift and align patching cadence with business risk appetite. Cloud‑native controls, combined with traditional on‑prem processes, enable a cohesive strategy that scales with hybrid workloads.
By treating cloud patch management and on‑premises patching as complementary streams rather than isolated efforts, organizations can enforce a common framework for testing, deployment, and compliance. This unified stance supports secure patching for hybrid environments, ensuring that updates are prioritized correctly and validated in representative environments before wide‑scale rollout.
Automation as the Enabler for Hybrid Patch Programs
Automation is the accelerator that makes hybrid patch management practical at scale. Automated discovery and inventory pipelines feed patch catalogs in real time, while continuous vulnerability scanning prioritizes patches by risk and impact. Automation also supports testing in production‑like environments and phased deployments, reducing manual toil and accelerating time‑to‑patch.
A mature automation strategy enforces policy‑driven patching that applies updates within defined windows, while surfacing noncompliant systems for remediation. Although automation speeds routine patching, human judgment remains essential for prioritization, validation, and exception handling, ensuring that the patching program aligns with cloud patch management goals and on‑premises patching best practices.
Testing, Validation, and Rollback in Hybrid Environments
Structured testing and staging are critical to preventing production disruptions in hybrid environments. Move patches through a controlled progression—from testing to staging to production—ensuring environment parity and representative workloads. Centralized testing helps catch regressions and confirms compatibility across operating systems, cloud platforms, and on‑prem software.
Rollback and recovery plans are non‑negotiable. Predefined rollback steps, validated backups, and tested restore procedures enable rapid remediation if a patch introduces issues or downtime. This discipline supports both cloud patch management and on‑premises practices, reinforcing a resilient strategy for security patching in hybrid environments.
Measuring Success: KPIs and Compliance for Patch Management in Hybrid Environments
Measuring patching success requires a balanced set of metrics that reflect both cloud and on‑prem realities. Track patch cadence adherence, time‑to‑patch for high‑risk assets, and patch success rates by environment and asset class. Monitoring downtime and performance impact helps quantify the operational effects of updates.
Compliance and governance are integral to sustaining momentum. Maintain audit trails, attestations, and change records for every patch action, including approvals and rollback events. Regularly review risk scoring, policy effectiveness, and security posture improvements to ensure ongoing alignment with regulatory requirements and business objectives in a hybrid landscape.
Frequently Asked Questions
What is a Cloud and On-Prem Patch Strategy and why is it important for hybrid environments?
A Cloud and On-Prem Patch Strategy is a unified approach to patch management that harmonizes updates across cloud-based and on-premises resources. In hybrid patch management, one governance model and one risk framework help reduce exposure, maintain compliance, and accelerate patch delivery without introducing downtime. The strategy emphasizes visibility, automation, and coordinated deployment to protect assets across cloud patch management and on-premises patching best practices.
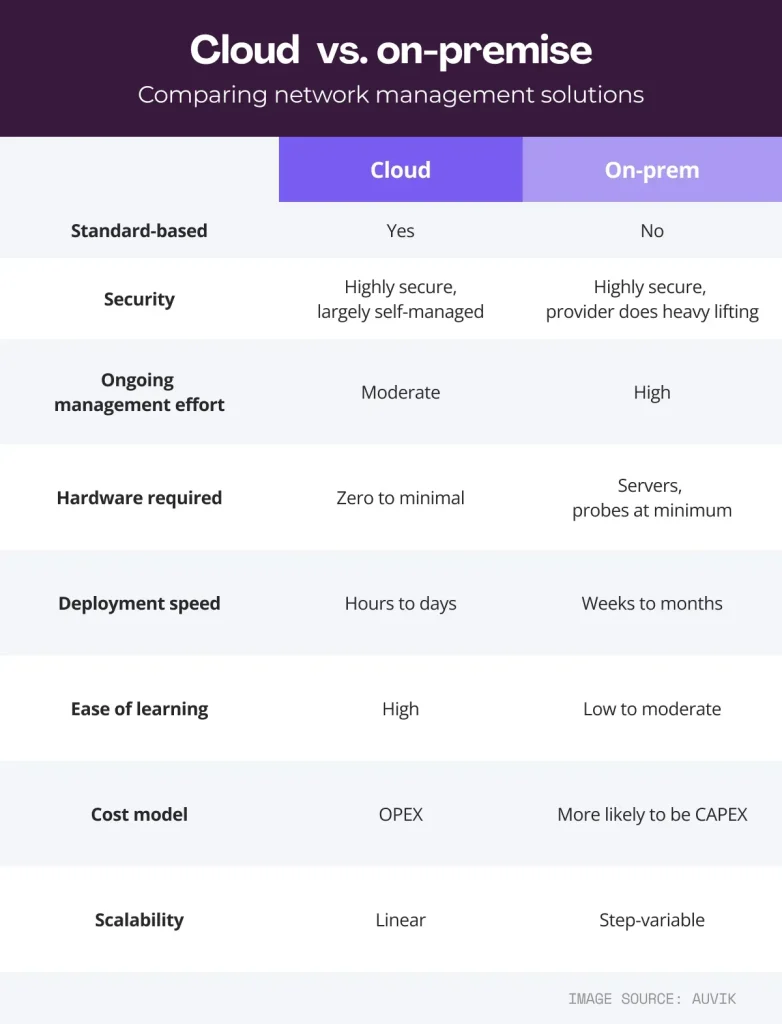
How does patch management in hybrid cloud environments differ from on-premises patching best practices?
In hybrid cloud environments, patch management focuses on automation, scalability, and platform-level updates delivered through cloud-native services, while on-premises patching emphasizes control, testing, and integration with existing tools. Cloud patch management must account for ephemeral workloads and managed services, whereas on-premises patching follows traditional change control and downtime planning. A unified Cloud and On-Prem Patch Strategy blends both approaches to maintain a single policy and risk taxonomy.
What are the foundational steps for inventory, visibility, and risk in a Cloud and On-Prem Patch Strategy?
Start with a complete view of all assets—cloud accounts, VMs, containers, storage, and on-prem servers—and maintain an authoritative CMDB or asset registry. Implement vulnerability management that prioritizes patches by exposure and business impact, and tie patch activity to an integrated change-management process. With a strong foundation for Cloud and On-Prem Patch Strategies, visibility becomes the heartbeat of security and reliability.
What role does automation play in enabling Cloud and On-Prem Patch Strategies?
Automation scales patching across hybrid environments without sacrificing control. It enables automated discovery and inventory, continuous vulnerability scanning, automated testing, and deployment pipelines with phased rollouts. Policy-driven enforcement ensures patches are applied within defined windows and noncompliant systems are surfaced for remediation, supporting both cloud patch management and on-premises patching best practices.
What practical framework can organizations follow to implement a hybrid patch program across cloud and on‑prem?
Adopt a practical, repeatable framework: define policy and scope, build a single source of truth, segment assets by risk, automate discovery, implement phased deployment, centralize testing, establish rollback, and monitor progress. Use blue/green or canary deployments for low-risk systems and expand to broader cohorts as confidence grows. This framework embodies Cloud and On-Prem Patch Strategies for secure, scalable delivery across hybrid environments.
How can organizations measure success and ensure compliance in security patching for hybrid environments?
Measure patch cadence, time-to-patch for high-risk assets, and patch success rates across environments. Track downtime, performance impact, and improvements in vulnerability scans to gauge security posture. Maintain compliance attestations, audit trails, and governance reporting to demonstrate control over Cloud and On-Prem Patch Strategies and security patching for hybrid environments.
| Topic | Key Points |
|---|---|
| Hybrid reality and patch challenge | Organizations run workloads across public cloud and on‑prem; patching must secure both without downtime; aim to harmonize updates, minimize exposure, and meet governance. |
| Governance, risk and automation | One governance model, one risk framework, and automation that scales; precise inventory, continuous vulnerability management, and coordinated deployments. |
| Foundation: Inventory, Visibility, and Risk | Single truth for the estate: asset discovery, authoritative CMDB, vulnerability management, and integrated change management; visibility enables risk scoring and deployment pipelines. |
| Core components of a robust patch strategy | Standardized patch policy; tiered testing; automatable patch delivery; rollback/recovery; compliance and auditing. |
| Hybrid Cloud vs On‑Prem patching | Cloud focuses on automation, scalability, and platform updates; on‑prem emphasizes control, testing, and change management; aim for a unified life cycle. |
| Automation as the Enabler | Automated discovery, real‑time vulnerability scanning, automated testing, phased deployments, and policy‑driven enforcement; human judgment remains for prioritization and exceptions. |
| Practical Framework for a Hybrid Patch Program | Policy and scope; single source of truth; risk‑based asset segmentation; automate discovery; phased deployment; centralized testing; rollback readiness; monitoring and reporting; continuous improvement. |
| Security and Compliance Considerations | Timely patching for critical vulnerabilities; regulatory compliance reporting; least privilege and secure channels; audit trails for every action; regular stakeholder risk communication. |
| Measuring Success and Continuous Improvement | Track cadence adherence, time‑to‑patch for high‑risk assets, patch success rates, downtime impact, security posture improvements, and compliance attestations. |
| Common Pitfalls to Avoid | Patch drift between cloud and on‑prem; over‑patching or under‑patching; inadequate testing; weak rollback planning; fragmented reporting. |
| The Road Ahead | Future patches lean into smarter automation, deeper security tooling integration, and tighter CI/CD integration; orchestration across clouds and on‑prem data centers while preserving visibility, governance, and safe delivery. |
Summary
Conclusion: Cloud and On-Prem Patch Strategies describe a unified approach to securing and updating assets across hybrid IT environments. By combining comprehensive asset inventory, automated vulnerability management, and staged, policy‑based deployments, organizations can reduce risk, improve compliance posture, and boost resilience across cloud and on‑prem infrastructure. This descriptive conclusion emphasizes visibility, governance, automation, and safe, scalable patch delivery to help hybrid environments stay secure and adaptable as the business evolves.