Software patches are essential updates that defend your systems against evolving threats. They fix bugs, deliver security patches, and sometimes add minor enhancements to keep software reliable. Understanding how patches work helps individuals and teams apply them effectively and avoid downtime. A disciplined patch management approach reduces risk, improves reliability, and supports regulatory compliance. Prioritizing critical vulnerabilities and maintaining a steady update cadence highlights the importance of software updates and software patching.
From an information-security perspective, this concept is best described through patch updates, vulnerability remediation, and proactive update management. Web teams and IT pros talk about maintenance releases, security updates, and routine checks that keep software ecosystems resilient. By emphasizing testing in staging, phased rollouts, and monitoring, organizations reduce disruption while safeguarding data and uptime. In practice, the right cadence, automation, and governance turn patching from a reactive task into a strategic security control.
Frequently Asked Questions
What are software patches and why are they important for security and updates?
Software patches are small, targeted updates that fix bugs, close security vulnerabilities, and sometimes add or refine features. They are a key component of patch management and are critical for security patches and the overall importance of software updates, helping to improve reliability and reduce risk.
How do software patches work and get deployed across systems?
Software patches follow a lifecycle: discovery or disclosure, patch development, testing, release, deployment, and verification. Understanding how software patches work helps teams plan safe, timely updates and integrate patching into a broader patch management strategy.
What is patch management and how does it relate to software patches?
Patch management is the structured process of identifying, testing, deploying, and verifying software patches across devices and applications. It ensures that software patches are applied consistently and on schedule, reducing exposure to vulnerabilities and supporting the importance of software updates.
What is the difference between security patches and other patches in software patching?
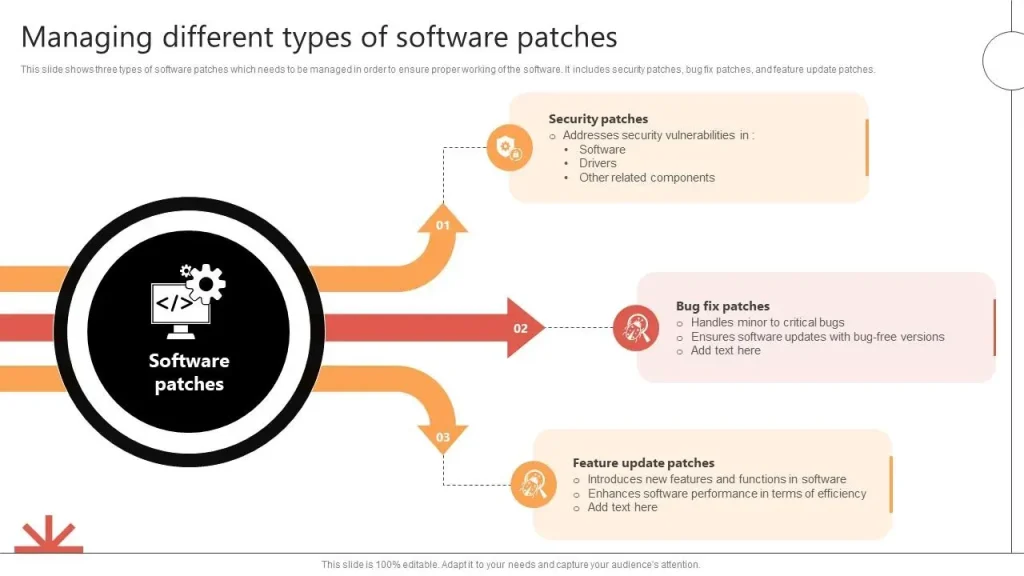
Security patches specifically fix vulnerabilities that could be exploited by attackers, making them the highest-priority category. Other patches address bugs, performance issues, or feature improvements. Together, they form a complete software patching strategy within patch management.
What are best practices for applying software patches in organizations?
Best practices include maintaining an up-to-date software inventory, prioritizing patches by risk, establishing a testing process, scheduling regular patch windows, and automating where possible. Use staged rollouts, verify patch success, document changes, and have rollback plans to minimize disruption.
What are common challenges of software patching and how can I minimize downtime?
Common challenges include downtime requirements, compatibility risks, patch fatigue, and testing needs. Mitigate them with phased rollouts, backups, rollback plans, thorough testing, and proactive monitoring to ensure patches install cleanly and systems stay available.
| Aspect | Key Points |
|---|---|
| What are software patches? | A small, targeted update applied to a program or operating system to fix problems. Patches address bugs, improve performance, fix security vulnerabilities, resolve compatibility issues, and may add or refine features. They fall into major categories: security patches, bug fixes, and improvement patches. |
| Security patches vs. other patches | Security patches fix vulnerabilities that could allow unauthorized access, data leakage, or system compromise and are the highest priority. Bug fixes and improvement patches enhance reliability and user experience but are less urgent. A solid patching strategy prioritizes security patches while maintaining regular non-security updates. |
| How patches work: high-level flow | Discovery and disclosure of issues → Patch development → Testing and QA → Release and distribution → Deployment and installation → Verification and monitoring. |
| Patch management definition | A structured process to acquire, test, apply, and verify patches across hardware and software within an organization, ensuring timely and consistent updates with minimal disruption. |
| Why patches matter (business and security case) | Security: closes vulnerabilities; Compliance: meets regulatory requirements; Reliability and performance: fixes bugs; Compatibility: addresses ecosystem changes; Cost of inaction: breaches and downtime can be far more costly than patching. |
| Challenges and considerations | Downtime or maintenance windows; Compatibility risks; Patch fatigue from frequent updates; Testing requirements; Change management across departments and environments. |
| Best practices for effective patch management | Maintain up-to-date inventory; Prioritize by risk (especially critical security patches); Establish testing environments; Schedule regular patch windows; Automate where possible; Implement staged rollouts; Verify post-deployment; Have rollback plans; Monitor and update. |
| Practical tips for individuals/small teams | Enable automatic updates where suitable; Regularly check vendor/update channels for security patches; Prioritize patches for high-severity vulnerabilities; Back up data before patching; Test patches on non-production devices when feasible. |
| Broader context: patches vs updates | Patches are a subset of software updates focused on fixing vulnerabilities and bugs; updates may add features or changes. A mature program treats patches and updates as an ongoing cycle with regular review, testing, and application. |